Yext Social is the social media management platform for local engagement trust. Scaling localized, brand-approved social content to grow your customer base. Yext Social helps organizations engage meaningfully and foster ongoing growth at the community level.
DataParser offers a highly adaptable solution, with options for both cloud-based and on-premise deployments. Many configuration options and comprehensive feature sets ensure that organizations can tailor the system to meet a wide range of compliance, security, legal, and business requirements.
Yext Social DataParser ensures that all your relevant social media interactions and content are managed securely and can be retained in easily reviewed formats.
Additional social media sources are being considered for the Yext DataParser connectors including major networks like Google, Facebook and Instagram.
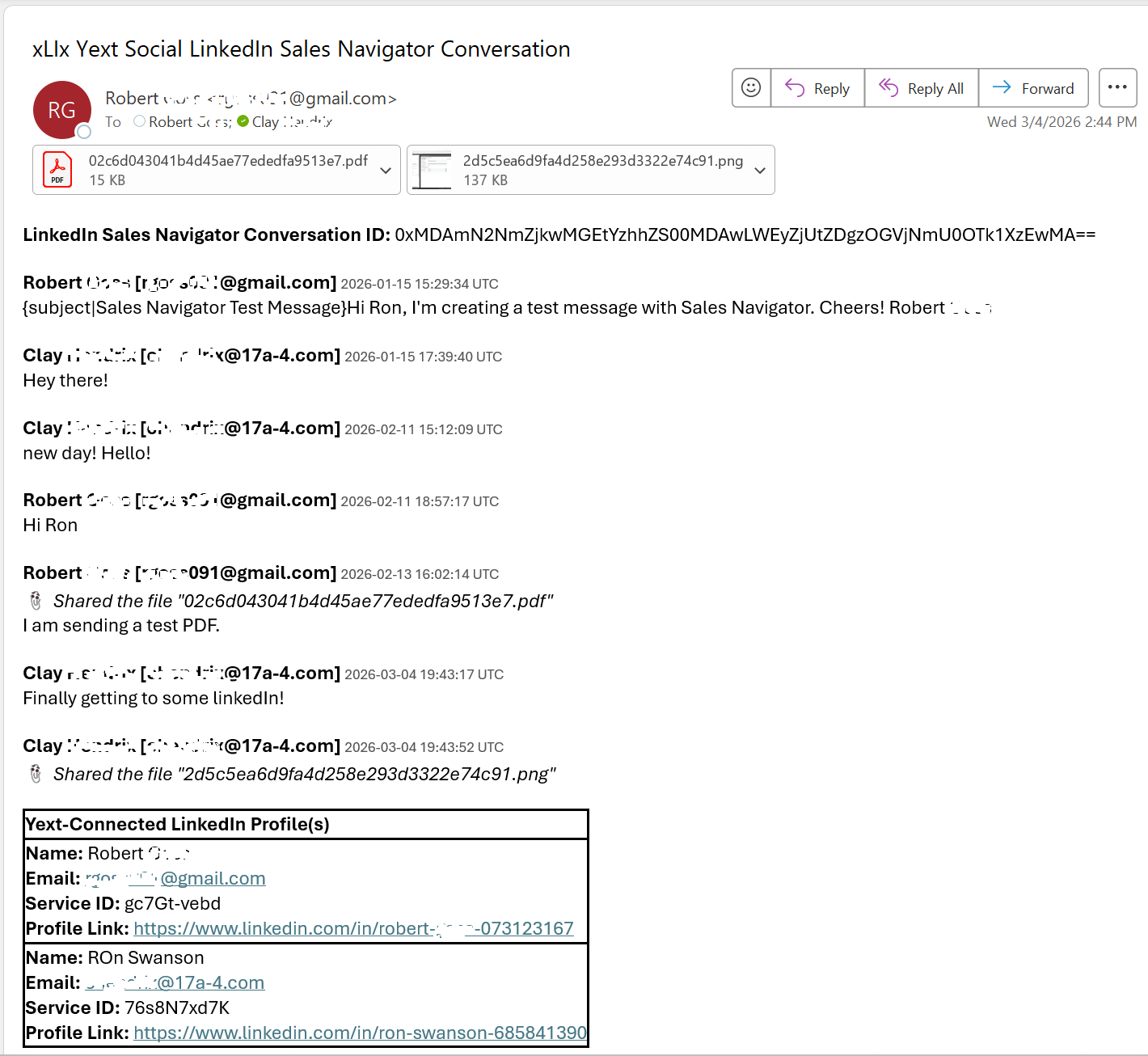
DataParser streamlines compliance processes by automating the collection, formatting, filtering and delivery of data for retention, archiving, and supervision of LinkedIn communications and interactions. This automation eliminates the need for manual intervention, allowing organizations to efficiently meet regulatory requirements without dedicating extensive resources to manual tasks.
By capturing all relevant communications, DataParser ensures that organizations have complete records available for audits. This comprehensive collection of data helps reduce compliance and legal risks, providing peace of mind that all necessary information is readily accessible when needed.
The DataParser enhances operational efficiency by facilitating the seamless transfer of social media data from LinkedIn and Yext Social to archives, eDiscovery systems, or analytics platforms. This streamlined data flow enables organizations to manage and use their LinkedIn information more effectively, supporting a wide range of business operations.
Security is a core feature of DataParser. With built-in encryption and access controls, the solution protects sensitive information throughout every stage of the data lifecycle. Organizations can trust that their communications and documents remain secure from unauthorized access.